Google Collection Phishing

By Jeremy Fuchs, Cybersecurity Researcher/Analyst at Check Point Software Company
Introduction
Google Collection is a cool tool that allows you to save links, images and videos and share them with others.
In keeping with the spirit of the BEC 3.0 attacks, we’re going to highlight how hackers are using this tool to spread phishing. By leveraging the legitimacy of Google, hackers are able to hide malicious links within legitimate sites.
This BEC 3.0 attack is yet another way hackers are tricking users into giving up sensitive information.
In this attack brief, Harmony Email researchers will discuss how hackers are using Google Collection to share phishing links.
Attack
In this attack, hackers are utilizing Google pages to send links to fake cryptocurrency sites.
Vector: Email
Type: Credential Harvesting
Techniques: Social Engineering, BEC 3.0
Target: Any end-user
Email Example
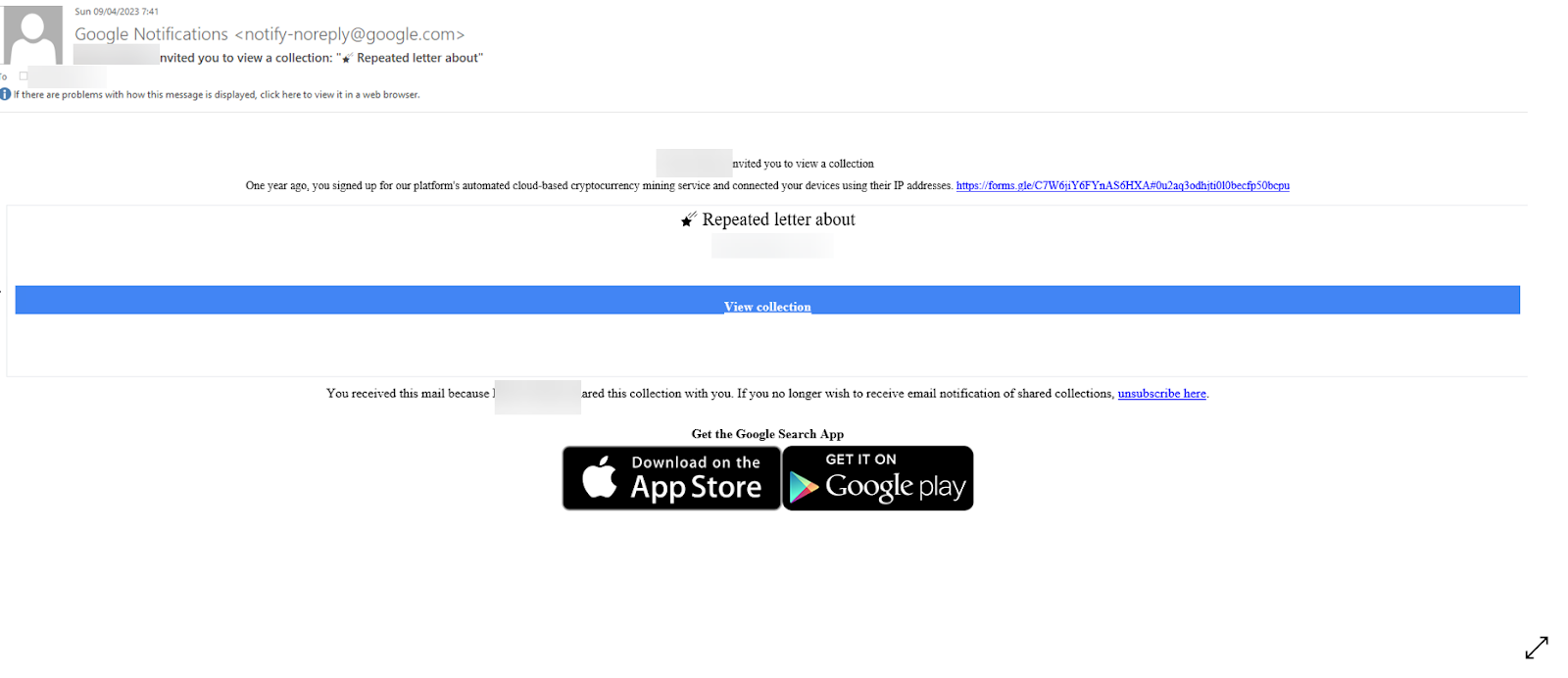
The first email comes in typical fashion, via a notification directly from Google. This is because the hacker shared the collection with the end-user. The email comes from a no-reply@google.com address. That address is legitimate and would be recognized as such by hackers and end-users alike. Clicking on the link is also okay–hovering over the URL will show a legitimate Googe link. Going to the page below is also, you guessed it, a legitimate Google page.
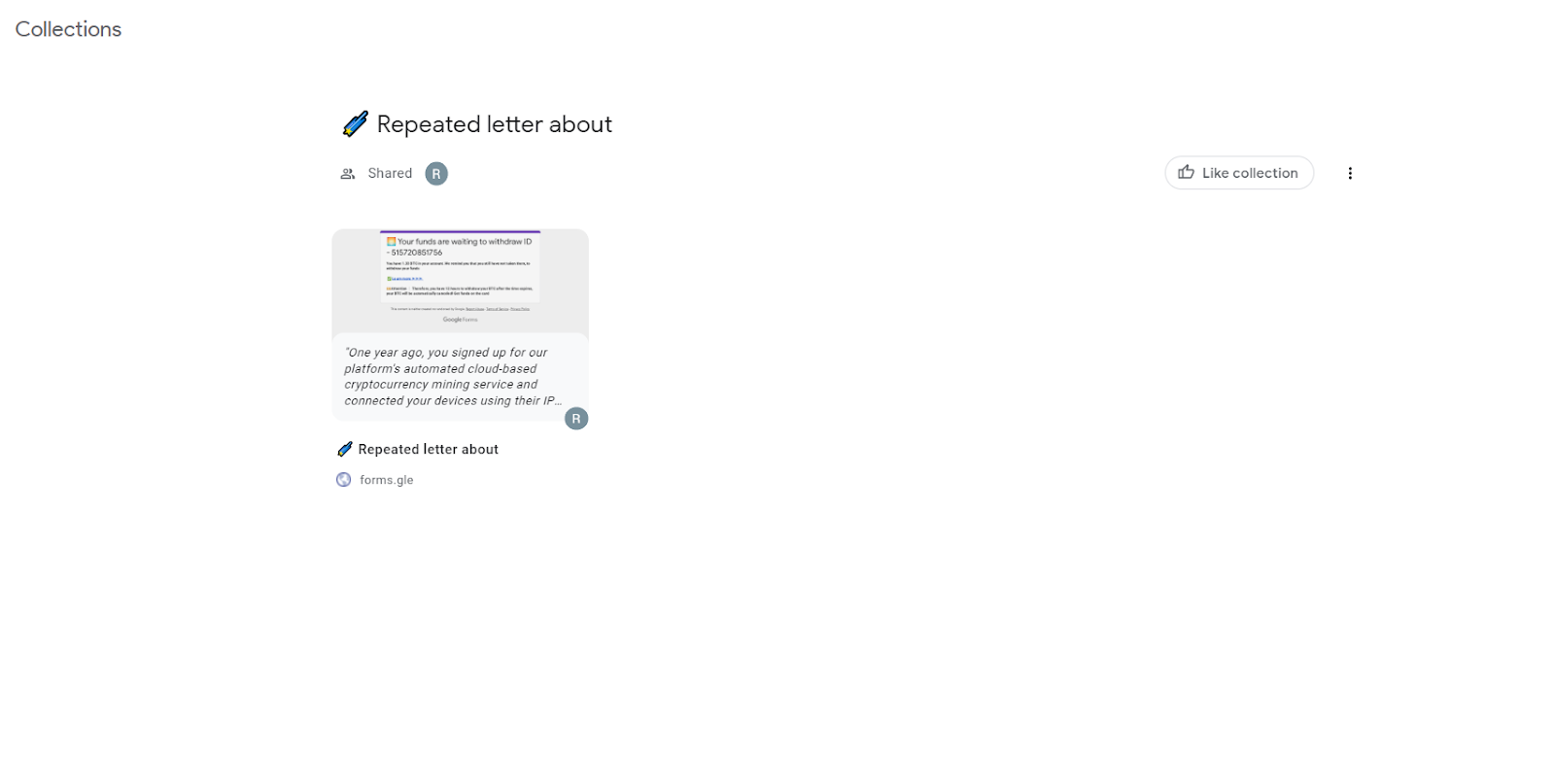
Google collections work like above, with a number of different card like figures. You can link to images, webpages, etc within that collection. Clicking on the card leads to the below page:
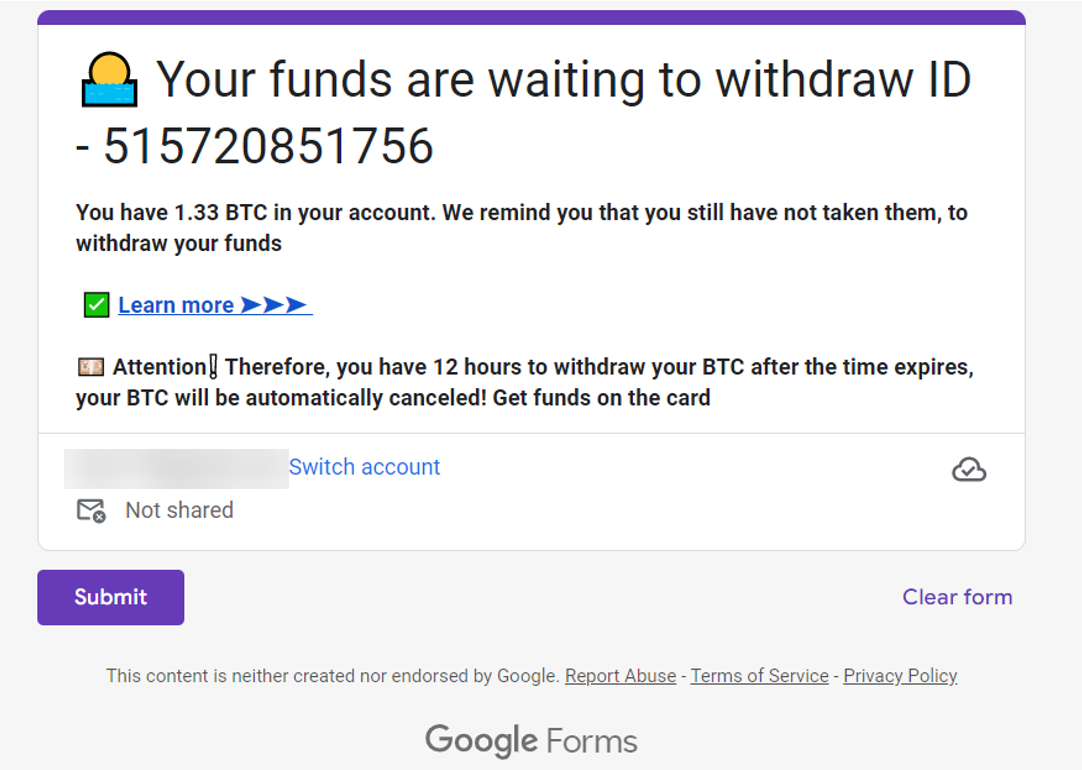
This is the link that they eventually want you to get to, which is a Google form. This will redirect to a fake cryptocurrency site, which will eventually steal money.
Techniques
The bottom of the Google page tells an important distinction: “This content is neither created nor endorsed by Google.”
What we’re saying here is critical: This isn’t to say that Google is now illegitimate or dangerous. Quite the contrary. But Google, like many sites, allow you to put any content on their page. Hackers are abusing this privilege by placing illegitimate, malicious sites.
To better ensure that their payloads get to their target, they are nesting it. It’s not in the first link in the email. It’s not in the second link that you click. It’s hidden in the third link.
So yes, end-users have to get through all these links and layers, and that’s certainly not a guarantee.
But when they see Google link after Google link, the hesitancy might start to drop. And when the guard drops, users might be more free-wheeling with their mouse clicks.
That’s the hope of BEC 3.0. It’s not trickery, but rather using what the user knows against them. Because it seems so standard–because it is so standard–users might be more willing to cooperate.
That, in turn, could lead to some real damages.
Check Point informed Google of this research on July 5th.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
Implement security that uses AI to look at multiple indicators of phishing
Implement full-suite security that can also scan documents and file
Implement robust URL protection that scans and emulates webpges
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.






























